- June 20, 2022
- Posted by: Admin
- Category: Competitive research, Malwares, News

We all have valuable information on the internet. That is why it is critical to be aware of the most recent ransomware cyberattacks in order to understand how hackers operate and thus remain one step ahead.
With a data breach costing an average of $3.86 million, businesses all over the world are looking for ways to avoid such an expensive outcome. Customers’ trust is lost as a result of breaches, in addition leading to monetary loss. A firm cannot hope to retain and develop its aims without the customer’s trust. Today’s biggest threat in the cybersecurity world is ransom attacks.
Ransomware, or cyber extortion, happens when malicious software infiltrates computer systems and encrypts data, keeping it hostage until the victim pays a ransom. It is a type of crypto virology virus that threatens to expose or permanently restrict access to the victim’s personal information unless a ransom is paid. While some ransomware uses a technique known as crypto viral extortion to lock the system in a way that is straightforward to reverse for a knowledgeable user, more complicated viruses utilize a technique known as crypto viral extortion.
The victim is duped into downloading or opening a Trojan that is disguised as a genuine file and sent as an email attachment, leading to a ransomware assault. The WannaCry ransomware, for example, spread automatically between computers without any human intervention.
Here are five different forms of Ransomware:
- Crypto Locker: The Crypto locker botnet is one of the oldest types of cyber-attacks, dating back over two decades. In 2013, hackers used the original Crypto Locker botnet approach in ransomware, resulting in the Crypto Locker ransomware. Because it employs strong encryption methods, Crypto Locker is the most devastating type of ransomware. Without paying the ransom, it is often difficult to decrypt (rescue) the Crypto ransomware-infected machine and files.
- WannaCry: A serious Microsoft flaw was exploited to create a worldwide ransomware worm that infected over 250,000 computers before being halted by a kill switch. WannaCry is released as a dropper, which is self-contained software that extracts the encryption/decryption application, encryption key files, and the Tor communication program. It is not disguised and is pretty simple to find and remove.
- REvil: REvil was established by a group of opportunistic assailants. It collects data before encrypting it, allowing targeted victims to be blackmailed into paying the ransom if they refuse to hand over their personal information. The attack was started by infected IT management software that was used to patch Windows and Mac computers.
- Ryuk: Ryuk is a ransomware malware that is propagated by hand and is primarily used in spear-phishing attacks. Reconnaissance is used to select targets with diligence. All data on the infected machine is encrypted, and email messages are sent to pre-selected victims.
- Bad Rabbit: Bad Rabbit was well-known ransomware that appeared to be targeting Russia and Ukraine, primarily affecting media companies. It was suspected to be related to Not Petya since it spread using the same code and exploited the same vulnerabilities.
What to do when your organization is under Ransomware Cyber Attack??
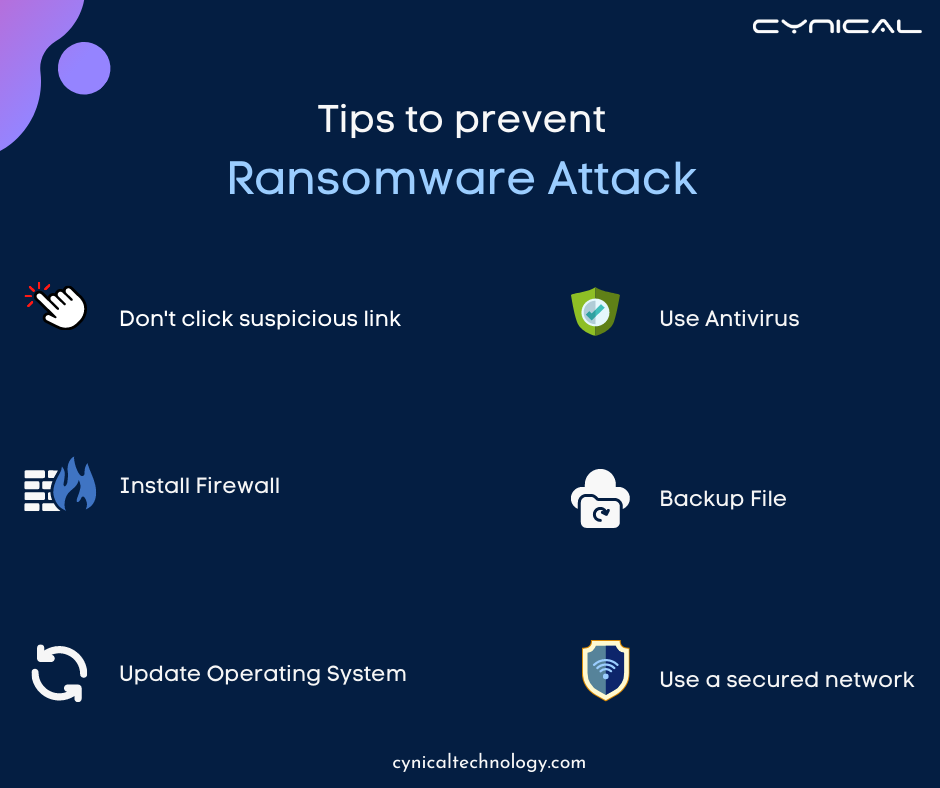
Having a disastrous incident, such as a Cyber Attack on your firm, can be a curse, depending on the outcome and how you respond to it. To avoid being infected with ransomware, you may take a number of precautions.
- Pull off the WAN connectivity: Disconnect the Core switch immediately if you have numerous locations connected via MPLS or SDWAN. Malware payloads may download more script files and target IP segments across several places. This action will mitigate the effects of Ransomware infection in all sites.
- Install Norton antivirus software: Install Norton antivirus software to detect and prevent dangerous malware like ransomware from ever starting, as well as whitelisting software to prevent unapproved apps from ever executing.
- Service backups and restoration: Begin by ensuring that all critical data (both structured and unstructured) is backed up (Disk or tapes). If the data of a crucial application or file share is being encrypted due to a cyber-attack, create a priority list and begin restoring the data as soon as possible. The hacker team may have gained access to the backup server and purged the tapes stored in the library.
- Take a sample of an infected system’s logs: Collect and share the logs requested by the anti-virus OEM from the infected machine (first isolate it). They will release a hot-fix patch to protect additional systems from becoming infected and to halt the spread of the virus (Ransomware kind of infection).
Notes
- Never click on any dubious links
- Do not open suspicious email attachments
- Keep your programs and operating system up to date
- Use VPN services on public Wi-Fi networks