Web Applications Security Testing
Web applications are #1 attack vector for malicious individuals. We evaluate vulnerabilities of web apps by looking for security and configuration problems with the Web and application servers and operating systems of the applications.
Mobile App Security Testing
Mobile has become a primary device for information storage. We provide you with a detailed security analysis of your phone app and help to ensure that there aren’t any loopholes in the software that may cause data loss.
Network VAPT
We Protect your Network from Internal and External Threats. In today’s market circumstances, no one can afford to lose a single confidential information or data. However, online businesses are always at risk. Therefore, it is vital to identify all the potential danger and get them fixed.
Risk Assessment
We gather and identify information and information systems, analyze it, and assign risk ratings to your information systems. Our risk assessment service will provide you with a clear picture of your security vulnerabilities and give you specific recommendations for remediations.
Incident Response
Incident response services help you prepare for, manage, and recover from data breaches and network attacks. Our security experts proactively hunt and respond to threats and apply the latest threat intelligence before breaches occur.
Training and Consulting
We offer training courses and consulting services. We are well known for our threat-based perspective and straightforward recommendations.
CMS Security
We update the service with new vulnerabilities every week, making sure your scan covers the latest security issues in the CMS (Drupal, Wordpress, Joomla) you are using.
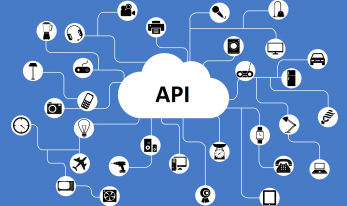
Web Service Assessments
Security is critical to web services. Our web service assessment test focuses on Web Service Request and Response model.
Secure SDLC Guidance
The security we provide incorporates all the security assurance activities like penetration testing , code review and architecture analysis involved in a secure SDLC Process.
Is your Website Secure?
- Scan for SQL injection, XSS, others additional vulnerabilities
- Provide IT security auditing of organization.
- Find and report vulnerabilities in web applications.
- Detect security loopholes in famous CMS like WordPress, Joomla, Drupal, etc.
- Provide System/OS hardening services.
- Protect systems against OWASP Top 10 Vulnerabilities.
- Provide Security Consulting services.
- Detect semantic errors in code.
- Train employees/staffs against all possible security threats.