- April 4, 2022
- Posted by: Cynical_Technology
- Category: Case Study, News
The activity we have ascertained is attributed to a threat group named DEV-0537, also known as LAPSUS$ as tracked by Microsoft. Lapsus$ has recently conducted numerous attacks against the enterprise, including those against NVIDIA, Samsung, Vodafone, Ubisoft, Mercado Libre, and now Microsoft. This month they were in the headlines for their major data breaches. And here’s why.
- The Lapsus$ hacking group claims to have leaked the source code for Bing, Cortana, and other projects stolen from Microsoft’s internal Azure DevOps server.
- Okta, a major provider of access management systems, says that 2.5%, or approximately 375 customers, were impacted by a cyberattack claimed by the Lapsus$ data extortion group.
- Samsung confirmed a data breach on its systems and that the intruder had access to source code used in Galaxy smartphones.
- Vodafone Portugal suffered a cyberattack causing country-wide service outages, including the disruption of 4G/5G data networks, SMS texts, and television services.
- Video game developer Ubisoft has confirmed that it suffered a ‘cyber security incident’ that caused disruption to its games, systems, and services.
- NVIDIA confirmed that they suffered a cyberattack that allowed threat actors to steal employee credentials and proprietary data.
Microsoft (MSFT) Has confirmed it was breached by the hacker group Lapsus$, adding to the cyber gang’s amplifying list of victims. Microsoft has scrutinized colloquial tactics being deployed to hack into the computer systems and networks of multiple organizations.
South America-based Lapsus$ is known for publicly posting notorious details about their hacks and sharing screenshots of stolen data on platforms such as Telegram and Twitter. Likewise, the group used the previously gathered information (for example, profile pictures) and had a native-English-sounding caller speak with the helpdesk personnel to enhance their social engineering lure.
The overt concerns around privacy and security issues in the digital world remain incommodious to only a few ‘tech-aware’ companies. As new attack momentum emerges, they’ll require a fundamental rehabilitation of today’s security paradigms to identify, verify and secure the company.
South America-based Lapsus$ is known for publicly posting details about their hacks and sharing screenshots of stolen data on platforms such as Telegram and Twitter. Here’s a look at what this latest cybersecurity issue is all about.
How does DEV-0537 target data exfiltration and destruction of organizations?
- Deploying the malicious Redline password stealer to obtain passwords and session tokens
- Purchasing credentials and session tokens on criminal underground forums
- Searching public code repositories for exposed credential
- Paying employees at targeted organizations (or suppliers/business partners) for access to credentials and multi-factor authentication (MFA) approval
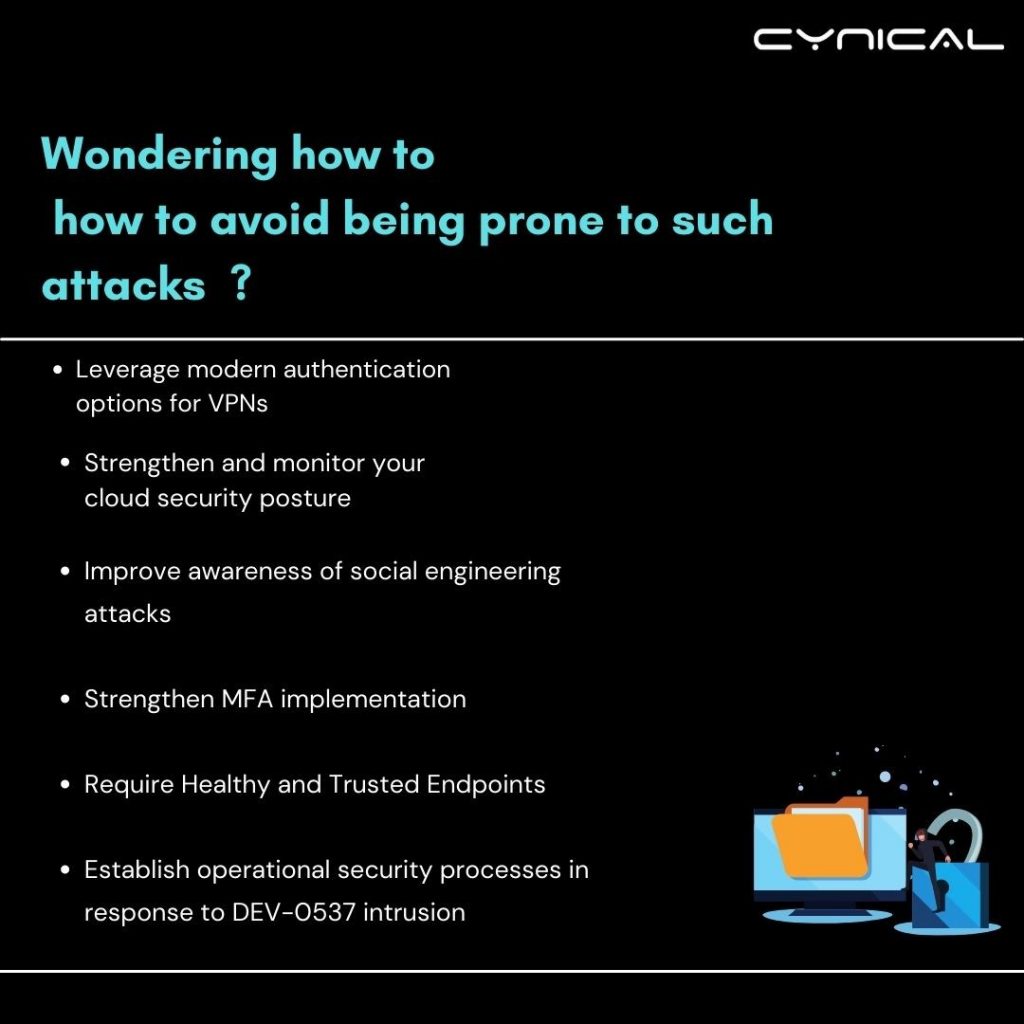
Here’s a quick guide on how to avoid being prone to such attacks
- Leverage modern authentication options for VPNs
- Strengthen and monitor your cloud security posture
- Improve awareness of social engineering attacks
- Strengthen MFA implementation
- Require healthy and trusted endpoints
- Establish operational security processes in response to the DEV-0537 intrusion
How to adopt healthy internet habits and protect digital privacy??
By making simple changes to your devices and accounts you can pilot unwanted access to your data. Protect your data and protect your privacy from whom you do not consent.
Data breaches and password leaks have been sprouting in the past decades. Many companies have been struck by hacker groups. If your company has different online accounts, there’s a high possibility that hackers have likely leaked data from at least one of them. If any of your accounts have been compromised, you can cross-reference on a website like have i been pwned? .
Hacker groups track everything you do on your website. They collect your website patterns, all personal information which would increase the chances of you being the next victim. Protect your web browsing to prevent malware attacks and if are victim of data breach ;
- Determine what was stolen
- Change password immediately and replace it
- Don’t click or install sketchy attachments
- Report it to the concerned department immediately
- Update software and devices.
Technology has made our lives easier. But it also means that your data is no longer your own. To prevent cyberattacks and data breaches you must prioritize cybersecurity and use services allied to it I.e. web application security testing, mobile app security testing, network VAPT, risk assessment, secure SDLC guidance.